What is IGA?
Identity governance is the policy-based centralized orchestration of user identity management and access control. Identity governance helps support enterprise IT security and regulatory compliance.
IGA combines Identity Governance and Identity Administration. IGA tools manage digital identity and access rights across multiple systems. To accomplish this, IGA tools aggregate and correlate disparate identity and access rights data that is distributed throughout the IT landscape to enhance control over user access. IGA tools have evolved over the years to support a broad and deep range of capabilities.
As a result, today’s IGA solution must address the needs of the modern workforce across all these vectors.
The Need for IGA
By 2023, 75% of security failures will result from inadequate management of identities, access, and privileges—up 50% from 2020. Source: Gartner
Identity governance and administration tools help simplify and streamline user identity lifecycle management through capabilities such as password management, integrations, automation, access request management, detailed event logging, provisioning and de-provisioning, and entitlement management.
According to Gartner, a new category of SaaS-delivered, converged identity, and access management platforms will be the preferred method for identity governance, access management and privilege access management by 2023.
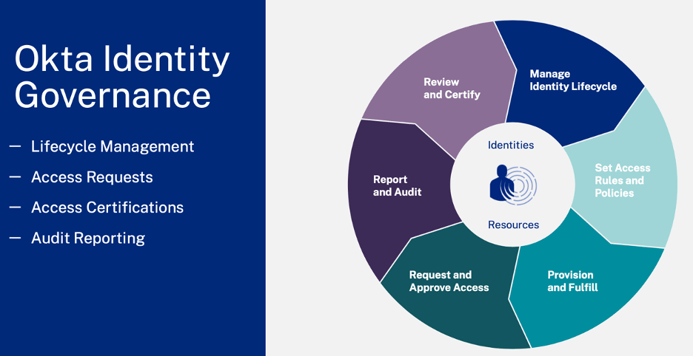
Features of Okta IGA
Okta IGA provides self-service Access to resources via common tools like Slack and in addition, we provide an approval request for sensitive application data and tools. Workflow tools provide customization. Okta IGA provide modern end user experience over mobile and chat.
Help IT team scale with more automation, delegation, and self-service. Okta IGA helps organizations drive better security and compliance outcomes. Making end user experience better. Getting access to things better. It is for all organizations of all sizes including new IGA users and existing IGA users to modernize.
Okta IGA features include:
-
Okta Access Requests: Simplify and automate the process of requesting and approving access to applications and resources. Self-service capabilities, tightly integrated with popular collaboration tools, meet users where they are, delivering a streamlined, frictionless experience to auto-provision their access.
-
Okta Access Certifications: Create and manage access review campaigns. Periodically reviewing user access to critical resources, and approving or revoking access automatically, is essential for ensuring that all users have the right level of access across all resources.
-
Enhanced Governance Reports: Out-of-the-box reporting capabilities to help meet audit and compliance requirements. Administrators can provide an audit report of who has access to what resources, who approved the access, and how they got it.
Benefits of Okta IGA
OKTA Identity governance provides enterprises with policy-based user identity management and access control. It supports their security and regulatory compliance efforts, enabling them to define, enforce, and review identity access management policies, map them to compliance requirements, and audit user access.
The primary features of identity governance include user administration, privileged identity management, identity intelligence, and role-based identity administration and analytics. Combined, these characteristics enable businesses to automate workflows, manage user permissions, stay compliant with data security regulations, and scale their organization.
- Simplify access governance with a unified IAM and governance solution that provides an unparalleled comprehensive view of every user’s access patterns.
- Secure your enterprise by gaining visibility and control into who has access to which digital resources in your organization.
- Improve IT efficiency by automating access approvals, provisioning, and remediation to reduce cost and eliminate errors.
- Integrate with your best-of-breed solutions stack for intelligent, efficient, user-friendly identity governance that provides quick time-to-value. Orchestrate access governance to reduce management workload with automated tasks and process workflows

Conclusion
IGA improves visibility into what users can and can’t access, which helps IT admins to streamline identity management and access control, efficiently mitigate risk and protect business-critical systems and data.
Reach out to your Active Cyber Sales rep for a demo and more information.
