August 2, 2023
The Power of RBAC in Azure: Safeguarding Your Resources with Precision
Written by: Sneha Patel
In today's interconnected digital landscape, cloud computing has become the backbone of modern business operations. As organizations increasingly shift their workloads to cloud platforms like Microsoft Azure, the importance of robust Identity and Access Management (IAM) security becomes paramount. One of the most effective tools in securing cloud resources is Role-Based Access Control (RBAC). In this blog, we'll explore the benefits of RBAC in IAM security in Azure and how it empowers organizations to implement precise access controls and fortify their data against potential threats.
Understanding Role-Based Access Control (RBAC)
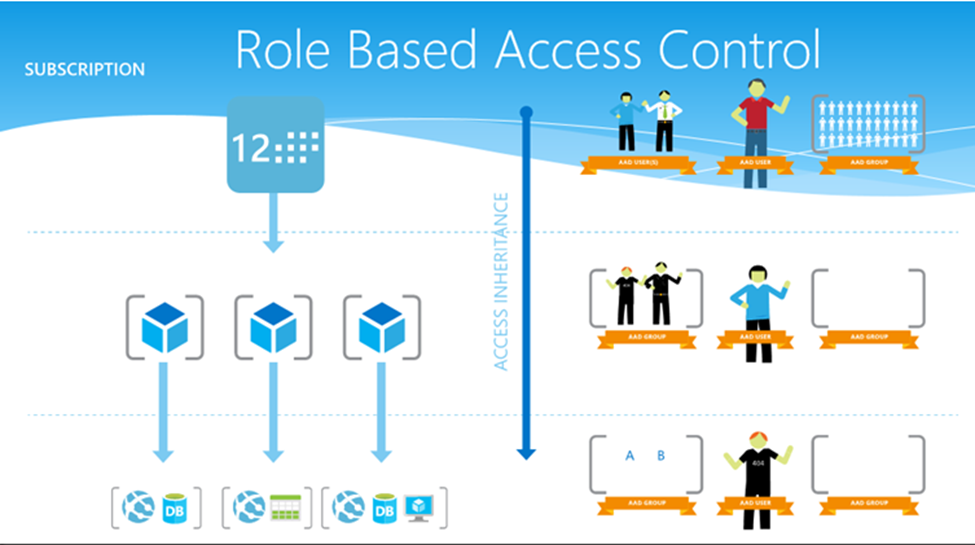
RBAC is an authorization mechanism that defines and manages access to Azure resources based on predefined roles. Instead of providing direct permissions to users, RBAC assigns users to roles, and those roles come with specific permissions. This approach ensures that users only have access to the resources they need to fulfill their responsibilities, reducing the risk of accidental or intentional data breaches.
Advantages of RBAC in Azure's IAM security:
- Fine-Grained Access Control - RBAC allows organizations to exercise fine-grained control over access permissions. With a vast array of built-in roles and the ability to create custom roles, administrators can tailor access rights to align with individual job functions. This granularity ensures that users can perform their tasks without gaining unnecessary privileges, thus minimizing the potential damage caused by malicious or accidental actions.
- Simplified Access Management - Traditional access management methods often require administrators to manually configure permissions for each user, making the process prone to errors and time-consuming. RBAC streamlines this process, as administrators only need to assign the appropriate roles to users, simplifying the overall access management. Moreover, when employees change roles or leave the organization, their access can be updated by modifying their role assignments, reducing the risk of stale or orphaned permissions.
- Strengthened Security Posture - By adhering to the principle of least privilege, RBAC enhances the security posture of Azure resources. Unauthorized access to critical assets becomes significantly harder for potential attackers, as they must first obtain the necessary role before gaining access to sensitive data or services. This proactive approach to security helps organizations stay ahead of potential breaches and mitigate risks more effectively.
- Compliance and Auditing - For organizations operating in highly regulated industries, compliance with industry standards and government regulations is a top priority. RBAC facilitates compliance by providing a transparent and traceable access control system. With Azure's built-in auditing capabilities, administrators can monitor and review user activities, ensuring that access is always in line with company policies and regulatory requirements.
- Scalability and Flexibility - As organizations grow and evolve, so do their access management needs. RBAC's scalability and flexibility accommodate these changes seamlessly. Azure RBAC enables administrators to add new roles, modify existing ones, and create custom roles tailored to specific scenarios. This adaptability ensures that IAM security remains agile and responsive to the dynamic nature of modern business operations.
- Collaboration and Delegation - RBAC promotes efficient collaboration by allowing users to be assigned to multiple roles, each corresponding to their various responsibilities. Additionally, administrators can delegate access management tasks to specific users or groups, reducing the burden on central IT teams and empowering different departments to manage access to their resources independently.
Role-Based Access Control (RBAC) is an indispensable tool in Azure's IAM security arsenal. RBAC empowers businesses to safeguard their cloud resources effectively. As organizations continue to harness the potential of the cloud, embracing RBAC in their Azure deployments becomes a strategic imperative, reinforcing their defenses against potential security threats and establishing a solid foundation for secure, efficient, and collaborative operations.
Remember, IAM security is an ongoing process, and regularly reviewing and fine-tuning role assignments are crucial for maintaining a robust and resilient security posture in Microsoft Azure.
Microsoft has put together great documentation on best practices for Azure RBAC and Troubleshooting Azure RBAC provided below for reference.
Role-Based Access Control - Best Practices
Role-Based Access Control Troubleshooting
Reach out to our team of experts to learn more about the benefits of RBAC and how it can fortify your cloud resources against potential threats.
Tag(s):
Other posts you might be interested in
View All Posts
Okta CIC
4 min read
| July 7, 2023
Unmasking Identity Proofing: The Key to Secure and Reliable Digital Transactions
Read More
CIAM
4 min read
| July 13, 2023
Understanding CIAM: The Next Generation of Identity and Access Management
Read More
Okta IGA
6 min read
| January 2, 2023
